The Changing Nature of Risk Management … and the need to quantify your risk management approach
Companies today face all sorts of risks. Supply chain and third-party risk are now becoming a top of the house risk discussion topic due to Covid, Solar Wind, FireEye, and the Suez Canal incident. And this risk is only increasing as organizations strive to operate more globally, leveraging third parties, building dependencies and operating in an eco-system of mutual interdependency. This all results in business relationships becoming more complex – and complexity introduces more vulnerabilities, more threats and increased risks. Managing the risks associated with these relationships while not hindering business speed is a critical challenge for today’s leaders.
This challenge is only compounded as digitalization, globalization and significant improvements to supply chain management -technical capabilities such as multi-cloud platforms, blockchain, RFID tracking-. In this interdependent world, this larger set of supply chain, third party interactions result in the increased exchange of business sensitive data, including client and employee PII, introducing increased risk to the organization.
The challenge is to balance the business advantages and opportunities of a larger and more complex eco-system interactions with secure digital transactions, secure access and protected data.
To be truly optimized and to address these issues, companies are moving to a more quantitative approach to identify and reduce risks. To better understand their risk exposure and expected loss in supply chain risk, companies are striving to understand their threats. By understanding threats and threat actors, organizations can better understand threat actors’ capabilities, asset targets and potential impacts, the basic elements of risk management.
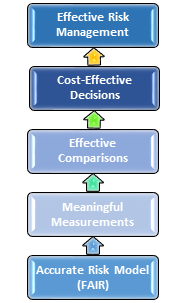
Additionally, we want to identify probable risks against the total population of possible risks. This is clearly both cost prohibitive and not particularly effective. To adjust to this ever-increasing complex operating environment, organizations today are turning to a quantifiable methodology to identify, manage and reduce risks. They are adopting the FAIR (Factor Analysis of Information Risk) model. Risk quantification using FAIR, allows us to decompose risk into the probability of a threat and the costs of that threat realised to an asset. By looking at risk in terms of Threats, Assets and Effect, all of which are measurable, we can quantify the impact of the risk(s).

And by quantifying the risk, we can now make fact-based decisions, based on cost / benefit analysis on which of our third-party relationships present the highest risks to our organization. By combining risk quantification with a mature and effective third-party risk management program, we can focus our resources on the highest of high-risk transactions and relationships.
We direct our investments to provide the best return (reduction of risks).
By adopting a quantitative risk-based approach, organizations are better equipped to focus their investments, address critical skill gaps, determine whether their control frameworks are effective and provide for business justification for their security spend. This results in actual risk reduction and it focuses investments on the top priorities.
Executives, boards, shareholders and regulators are demanding better risk management. And better risk management requires better data and a measurable framework. FAIR is based on the premise that effective risk management starts with these assumptions.
CISOs and CIOs can now provide their Board members and executive risk committee members with data-based answers to the following concerns:
-
Yes, we know our top risks and have quantified them. We have identified the degree of uncertainty with respect to a threat materializing.
-
We know the material impact if the risk event occurs
-
We know the expected loss, given the current residual risk
-
We have an understanding of the likelihood of an event occurring
-
We can provide a data-based business justification for managing those risks.
Our point of view is improved risk management requires better data on vulnerabilities, threats and risks across the enterprise and across the end-to-end supply chain. IBM Security has developed an integrated, risk-based, programmatic framework for managing third-party relationships and risks based on risk quantification.
Our goal is to embed security at each ecosystem layer, to protect the movement of goods and data in applications and on the cloud. The more organizations can address security risks and challenges in a quantitative manner, the more likely they will be effective in reducing risks. Afterall, the goal of risk management is to make better decisions under conditions of uncertainty that actually reduce risk.





