How can proper data privacy controls increase data value?
Data is widely touted as being the world’s most valuable commodity and the fuel for the next industrial revolution, but it’s only valuable if it’s shared and used – and that’s where things get tricky. How can I, as a data owner, know that my data is being used by people I trust, for aims I support and for which I’ve given permission? How do I know the data generated by my watch, my car, my phone, my dog (via his tracker, not directly) my doorbell, my heating controller…the list goes on…won’t be aggregated to build up a second-by-second account of my life. Nearly all of us now generate data for exactly that to be a real possibility.
On the flip side, companies have very good reasons to share and pool data and it becomes more valuable through doing so, but how can they be sure they are acting according to their mandate, that the data they share will be used properly and not copied (stolen), that it will be used for the purpose for which it’s given, and that they can prove all of this for compliance purposes, either for an external regulatory body or their own corporate governance?
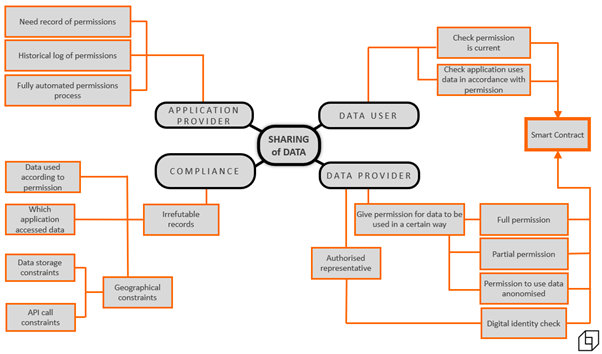
The key to the solution is to protect the data of the data owners from the data processors and ensure all parties are in control of what they share, they give permission for their data to be used only in a certain way, and above all they have irrefutable proof this is the case.
The “proof” can be written to logs of course, but the integrity of the logs is only as secure as the integrity of the people who control those logs. The challenge is to provide a system that all parties trust and none can change, alter or delete.
Data privacy companies such as Lockular solve this problem by encrypting the data then splitting it into very small packets known as “frades” which are then spread across multiple storage devices across several providers and geographies. Any frade by itself is completely meaningless as the process isn’t like shredding a document where any piece, no matter how small, is still recognisable. It is more akin to liquidising the document then putting spoonsful of the resulting glop across multiple storage platforms. The data then, is ultra-secured in transit and at rest.
To use the data it has to be reassembled by a precise process, every stage of which provides a checkpoint written to blockchain. Any attempt to bypass the process means the data is not reassembled correctly and so remains completely meaningless. This is the essential and irrefutable chain of custody, a record stored within blockchain of which application accessed the data, at what time, under which mandate and proof the data has only been used for the intended purpose. The record in the blockchain can not be changed or deleted – if it happened it stays happened. Obfuscated ephemeral keys unlock the data only for the minimum time necessary for the application to run and only the results of the data processing can leave the secure environment, ensuring the data itself can not be copied.
A practical application for this is in the Treasury Departments of multi-national companies operating across many countries with multiple subsidiaries - each a legal entity and usually each with several bank accounts. For the Treasurer to operate effectively, each subsidiary must instruct, or mandate, its many banks to share account data with the corporate Treasurer and in turn the Banks need to prove to their customer and regulator they’re sharing the correct data and in accordance with the customers’ mandates.
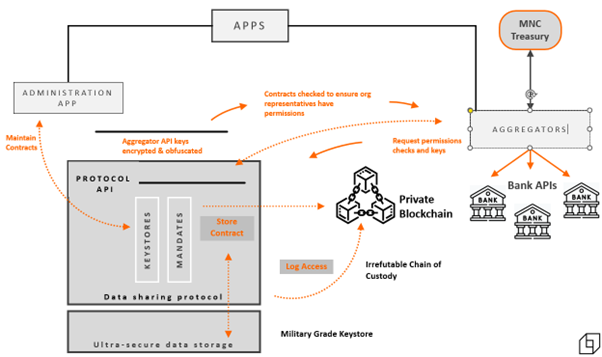
A process as shown above provides the security and irrefutable proof required for all parties to be certain they’re acting properly and that data remains secured. Banks are certain they’re acting according to their mandate, customers are certain their confidential information is secured and only used in accordance with their wishes, and Treasurers receive the data they need to drive informed business decisions. The irrefutable chain of custody written to the blockchain underpins all actions and provides the evidence needed by customers, banks and regulators alike.
This is a process for both protecting data privacy and maximising the value of data - one which all parties can trust as each is in control of what it shares, and with an irrefutable record to prove all parties have acted correctly.
About Lockular Limited:
Lockular’s patented inventions use homomorphic techniques to process encrypted data and spread over multiple storage platforms which can be geographically and provider diverse. A bad actor would need to breach multiple storage devices simultaneously, reassemble the data, then decrypt – a process which requires vast resources and is beyond nearly all actors. Lockular’s process uses blockchain technology to provide an irrefutable chain of custody and any attempt even to access the data is written to the blockchain, providing intrinsic intrusion detection.

Nick Evans
Nick Evans is the COO of Lockular Ltd, a company dedicated to digital privacy and securing the public cloud so we can all benefit from the undoubted economic and social benefits of a digital economy.
techUK - Getting Regulation Right for a Digital Society
Visit our Digital Regulation Hub to learn more or to register for regular updates.
techUK forums provide members the opportunities to showcase the ways in which they are helping to improve privacy and protect data protection rights. Our working groups, networks, and events - including our annual Digital Ethics Summit and Tech Policy Conference - enable cross-sector collaboration and are crucial sources of insight and thought leadership. Get in touch to see how we can support your policy work. Visit our Digital Regulation Hub and complete the ‘contact us’ form.


